Aug 15, 2022 | Live Compliance, Partner
HIPAA Training Standards Every Business Associate Needs to Know
Per the HIPAA Privacy Rule and HIPAA Security Rule, both Covered Entities and Business Associates, must require HIPAA training for all workforce members that access protected health information (PHI) or electronically protected health information (e-PHI) in any of its forms and should be provided “as necessary and appropriate for the members of the workforce to carry out their functions within the [organization].”
According to the Rule, training must be provided “to each new member of the workforce within a reasonable period of time after the person joins the [organization’s] workforce.” Along with all other annual compliance requirements, HIPAA training is arguably the most important. Your workforce members are your first line of defense in the event of a Breach and must be able to identify your organization’s designated HIPAA Security Officer, and have a firm understanding of the HIPAA Privacy and Security Rule. Training should also highlight the organization’s Technical, Administrative, and Physical Safeguard objective security requirements. It is best practice to provide ongoing security awareness training and, in addition to the mandatory annual training, the Privacy Rule also highlights what’s known as “periodic” training. The goal is to ensure workforce members’ knowledge of HIPAA compliance is not forgotten.
It’s advisable that HIPAA training is given to all employees as new hires during the new employee orientation period, and before new employees are exposed to or work with individually identifiable health information. This includes officers, agents, employees, temporary employees; like students, interns, volunteers, and salespeople. At a minimum, training should cover the basics of HIPAA, the basics of privacy and security requirements and restrictions, and policies and procedures. All new hires need to be provided HIPAA training and a post-test on the material covered within the training course to ensure comprehension of relevant and appropriate HIPAA policies and procedures. Security Officers should be trained on the Breach Notification Rule, Minimum Necessary Rule, and the Organization’s policies and procedures.
The HIPAA Privacy Rule states that “An [organization] must document that the training as described [in the HIPAA Text] has been provided.” Failing to do so will be seen as “willful neglect” and will result in HIPAA violations including monetary penalties as high as $1.5 million dollars. A minor violation may only result in a corrective action plan requirement, whereas a significant data breach attributable to a lack of training will be viewed more seriously.
At Live Compliance, we make checking off your compliance requirements extremely simple.
-
-
- Completely online, our role-based courses make training easy for remote or in-office employees.
- Short informative video training to meet periodic training requirements
- Depending on the size of your organization training may start as low as $79
Call us at (980) 999-1585 or visit us online at www.LiveCompliance.com/ezclaim
ABOUT EZCLAIM:
EZClaim is a leading medical billing, scheduling, and payment software provider that combines a best-in-class product with exceptional service and support. For more information, schedule a consultation today, email our experts, or call at 877.650.0904.
Jul 12, 2022 | Live Compliance, Partner
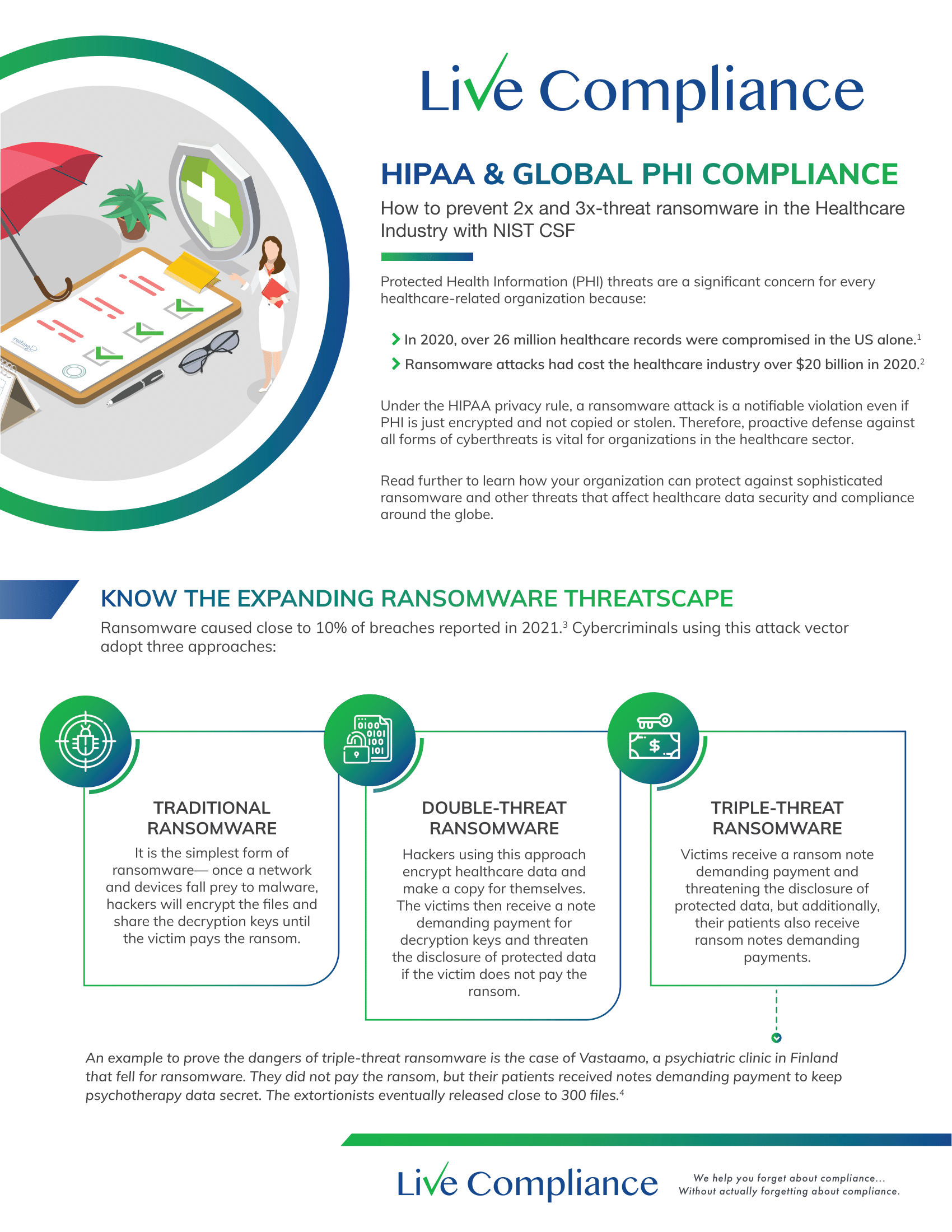
Whether you’re a one-person billing company or a multi-location organization, it’s possible that you’ve seen or heard of Malware and the potential risks associated with it and how it can cause major downtime and potential HIPAA violations due to breached information.
Criminals use malware to steal personal information, send spam, and commit fraud. Malware includes viruses, spyware, and other unwanted software that gets installed on your computer or mobile device without your consent. These programs can cause your device to crash and can be used to monitor and control your online activity. They also can make your computer vulnerable to viruses and deliver unwanted or inappropriate ads.
Here are a few, high-level quick steps you can take to spot and avoid Malware.
First, let’s talk security software.
Install and update security software, and use a firewall. Set your security software, internet browser, and operating system (like Windows or Mac OS X) to update automatically, and don’t forget to Back up your data regularly. Strong security software can prevent a hack or scam before it happens. You should install well-known software directly from the source. Sites that offer lots of different browsers, PDF readers, and other popular software for free are more likely to include malware. Read each screen when installing new software. If you don’t recognize a program or are prompted to install additional “bundled” software, decline the additional program or exit the installation process.
Don’t change your browser’s security settings and pay attention to your browser’s security warnings. Many browsers come with built-in security scanners that warn you before you visit an infected webpage or download a malicious file.
Next, watch what you’re clicking on.
Instead of clicking on a link in an email, type the URL of a trusted site directly into your browser. Scammers send emails that appear to be from companies you know and trust. The links may look legitimate, but clicking on them could download malware or send you to a scam site. Don’t open attachments in emails unless you know who sent it and what it is. Opening the wrong attachment — even if it seems to be from friends or family — can install malware on your computer.
Avoid clicking on pop-ups or banner ads about your computer’s performance! Scammers insert unwanted software into banner ads that look legitimate, especially ads about your computer’s health. Avoid clicking on these ads if you don’t know the source.
Your computer may be infected with malware if it:
-
- slows down, crashes or displays repeated error messages
- won’t shut down or restart
- serves a multitude of pop-ups
- serves inappropriate ads or ads that interfere with page content
- won’t let you remove unwanted software
- injects ads in places you typically wouldn’t see them, such as government websites
- displays web pages you didn’t intend to visit, or sends emails you didn’t write
Other warning signs of malware include:
-
- new and unexpected toolbars or icons in your browser or on your desktop
- unexpected changes in your browser, like using a new default search engine or displaying new tabs you didn’t open
- a sudden or repeated change in your computer’s internet home page
- a laptop battery that drains quicker than it should
At Live Compliance, we make checking off your compliance requirements extremely simple.
- Reliable and Effective Compliance
- Completely online, our role-based courses make training easy for remote or in-office employees.
- Contact-free, accurate Security Risk Assessments are conducted remotely. All devices are thoroughly analyzed regardless of location. Conducting an accurate and thorough Security Risk Assessment is not only required but is a useful tool to expose potential vulnerabilities, including those such as Password Protection.
- Policies and Procedures curated to fit your organization ensuring employees are updated on all Workstation Use and Security Safeguards in the office, or out. Update in real-time.
- Electronic, prepared document sending and signing to employees and business associates.
Don’t risk your company’s future, especially when we are offering a free Organization Assessment to help determine your company’s status. Call us at (980) 999-1585, or email me, Jim Johnson at Jim@LiveCompliance.com or visit www.LiveCompliance.com
For more information about DarkWeb breaches please contact us at (980) 999-1585 or email us at support@livecompliance.com

Jun 6, 2022 | Live Compliance, Partner
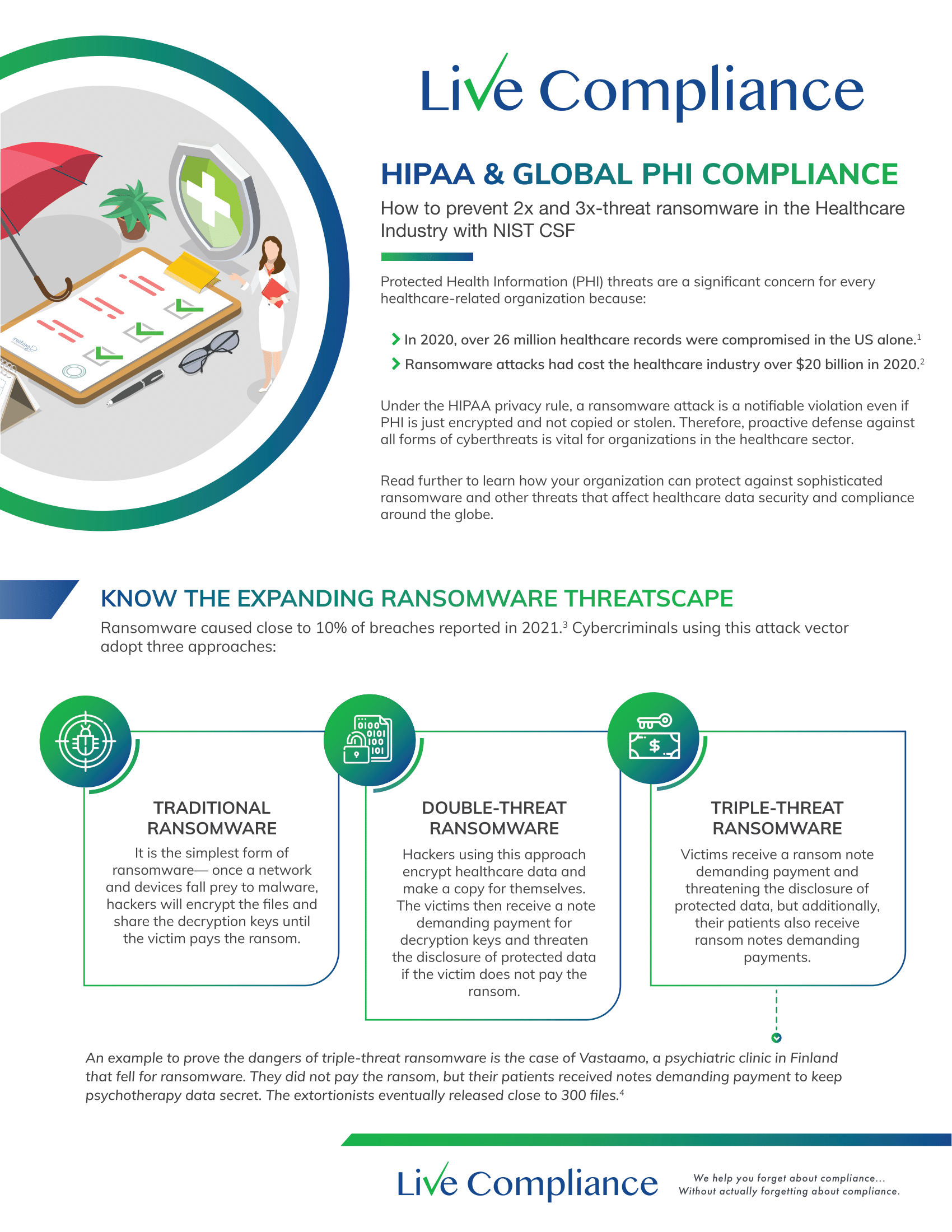
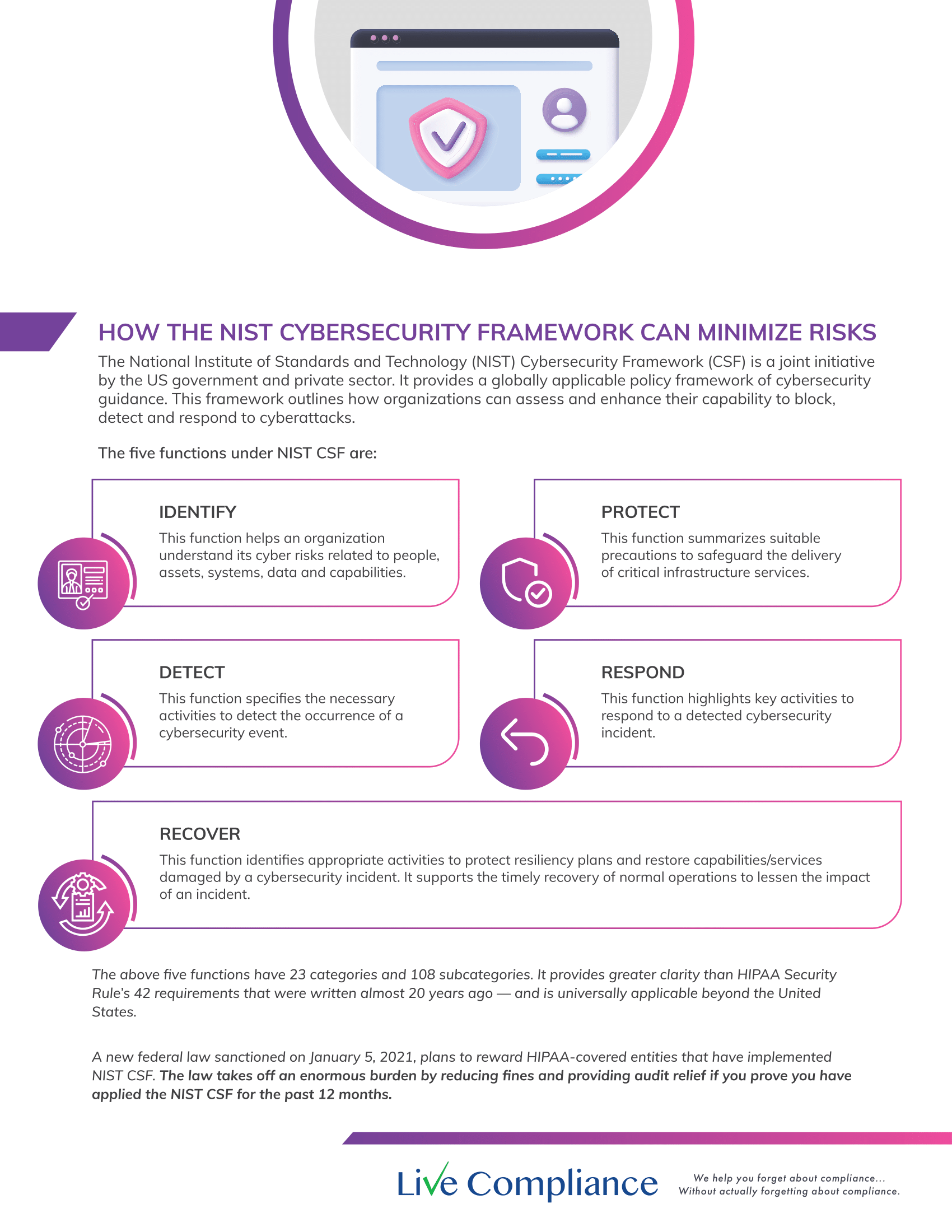
Complying with data privacy and protection regulations wouldn’t give several business owners sleepless nights if it only meant installing a predefined list of security solutions. Compliance goes way beyond this and for good reason. In principle, regulators, local or international, want businesses to:
- assess the type of data they store and manage
- gauge the potential risks the data is exposed to
- list down the remediation efforts needed to mitigate the risks
- undertake necessary remediation efforts regularly
- and most importantly, document every single step of this seemingly arduous process as evidence
Each of the above steps are mandatory and non-negotiable. A closer look will tell you that installing a list of expensive security solutions comes only after the first three steps in the process have been followed. Skipping past these initial steps and acting merely on presumptuous knowledge is tantamount to leaving your business’ future to sheer chance. It’s anyone’s guess what that would lead to.
That’s why we’re going to explain to you why a thorough and accurate risk assessment is truly the first step towards achieving compliance. Moreover, when repeated regularly, it can help you demonstrate continuous compliance while keeping cyberthreats at bay.
Security Risk Assessments Unearth Crucial Insights
A thorough and accurate risk assessment can unearth a host of crucial insights from even the deepest and darkest alleys of your IT environment to ultimately empower your decision making. Having actionable insights at your disposal can help you build strategies to reduce risk levels in practical ways instead of shooting in the dark by testing various tools.
Here are some of the most important details that become more apparent and unambiguous with every risk assessment.
Baseline of the System
A risk assessment helps you chart out the lifecycle of all data that is collected, stored and managed in your entire network.
Identification of Threats
A meticulous risk assessment identifies all the possible threats, such as intentional, unintentional, technical, non-technical and structural, that your business data is exposed to.
Identification of Vulnerabilities
With each assessment, you get the latest list of vulnerabilities prevalent in your network with respect to patches, policies, procedures, software, equipment and more.
Current Status of Existing Controls
From the assessment report, you can also understand the existing security and privacy controls protecting your business against vulnerabilities.
Probability of Impact
An accurate assessment report is fully capable of anticipating the probability of a threat that might exploit one of your network’s existing vulnerabilities.
Strength of Impact
Risk assessment also helps you gauge the possible impact of any threat hitting your business.
Imagine how easy it would be for you to build and implement a strategy to fix the security loopholes in your business while maintaining a well-documented record of your efforts.
Why Risk Assessment Is Needed for Compliance
While assessing whether you did everything in your capacity to ensure full compliance with the regulations, you also need to keep in mind that a regulator seeks evidence of compliance – documented reports. Besides helping you chart a successful path to compliance, a thorough risk assessment adds great weightage to demonstrating evidence of compliance. When you present the risk assessment reports along with other documentation, you demonstrate how your business carried out due diligence in upholding principles of data privacy and protection.
Please remember that no regulator expects you to have a fail-safe strategy. What matters is uncompromising intent, informed action and undeterred consistency. If you can demonstrate all this, you will most likely avoid any punitive action as well as a long list of problems could that surface afterwards.
Help Is Just a Conversation Away
Contrary to what is often claimed, there are no shortcuts to compliance or to any of the steps that lead to it. At the outset, achieving compliance might seem grueling. However, it isn’t as bad as it seems when due process and expert guidance is followed.
A conversation with us is all you need so we can help you walk through the complexities of risk assessment with diligent and customized guidance.

May 5, 2022 | HIPAA, Live Compliance, Medical Billing Software Blog, Support and Training
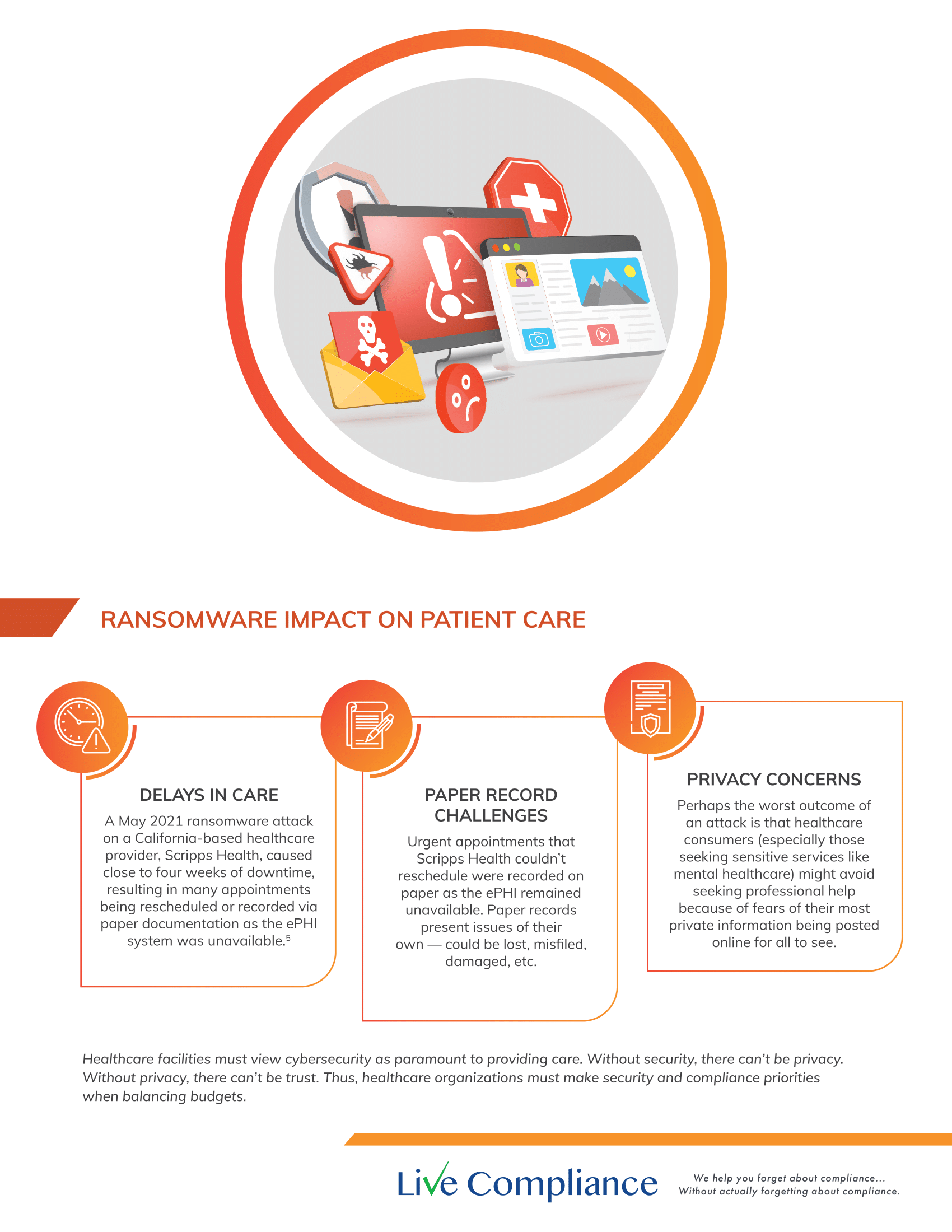
Your organization’s annual HIPAA Security Risk Assessment and Analysis are only one element of the compliance process, and whether you’re a Business Associate or Covered Entity, your organization must also “implement security updates as necessary and correct identified security deficiencies”. In other words, you must act via a Corrective Action Plan (CAP) following the required risk assessment process.
Here are a few common Corrective Action Plan steps:
- Implement technical policies and procedures to allow access only to those persons or software programs that have been granted access rights to information systems maintained.
- Implement procedures to regularly review records of information system activity, such as audit logs, access reports, and security incident tracking reports.
- Conduct accurate and thorough assessments of the potential risks and vulnerabilities to the confidentiality, integrity, and availability of ePHI.
- Develop a complete inventory of all its categories of electronic equipment, data systems, and applications that contain or store ePHI, which will then be incorporated into its Risk Analysis, and must complete a Risk Management plan.
What happens if I fail to complete my Security Risk Assessment?
Failing to complete your annual Risk Assessment oftentimes means the organization will be required to complete a “robust” Corrective Action Plan (CAP) and often with at least two years of monitoring activity.
Have you ever doubted whether a small billing company or independent physician practice actually ever face penalties?
Well, keep in mind, a Business Associate is a ‘person’ or ‘entity’. This means that there is no billing company too small to have to comply with the Federal HIPAA regulations. Again, if you have not completed an accurate and thorough security risk assessment prior to that, you could also be penalized under ‘willful neglect’. This category alone is $50,000 per violation!
It is important for you to understand that every complaint or potential breach must be investigated by HHS/OCR. If you, a billing company, or another vendor suspects a breach, you must inform the covered entity (your client) and have a breach risk assessment completed to determine key factors and take action.
An EZClaim partner, Live Compliance, will help you to make checking off your compliance requirements extremely simple. They provide:
- Completely online, our role-based courses make training easy for remote or in-office employees.
- Contact-free, accurate Security Risk Assessments are conducted remotely. All devices are thoroughly analyzed regardless of location. Conducting an accurate and thorough Security Risk Assessment is not only required but is a useful tool to expose potential vulnerabilities.
- Complete set of HIPAA Policies and procedures built directly into your portal. Includes actionability, change management documentation, and Incident Response Policy to assist with your Corrective Action Planning. Easily share policies with staff with one click.
- Built directly into your portal, easily monitor where your workforce may be vulnerable with our Dark Web Breach Searches. Easily expose breach sources with ongoing searching of active employee email or domain ensuring continued awareness of potential breach exposure. Weekly automatic email notifications if new breaches are discovered.
- Short, informative, privacy awareness videos covering technical, administrative, and physical safeguards with topics such as ransomware, phishing, the Dark Web, password protection, and more. All delivered monthly with no logins required, they empower your workforce to make conscious decisions when it comes to your organization’s privacy and security.
So, don’t risk your company’s future, especially when Live Compliance is offering a FREE Organization Assessment to help determine your company’s status. For more information, visit their website, e-mail them, or give them a call at 980.999.1585.
ABOUT EZCLAIM:
EZClaim is a medical billing and scheduling software company that provides a best-in-class product, with correspondingly exceptional service and support. Combined, they help improve medical billing revenues. To learn more, visit EZClaim’s website, e-mail them, or call them today at 877.650.0904.
[ Contribution by Jim Johnson with Live Compliance ]

Apr 11, 2022 | Live Compliance, Partner
As we’ve stressed before, your organization’s annual HIPAA Security Risk Assessment and Analysis are only one element of the compliance process.
Whether you’re a Business Associate or Covered Entity, your organization must also “implement security updates as necessary and correct identified security deficiencies”. In other words, you must act via a Corrective Action Plan (CAP) following the required risk assessment process.
Here are a few common Corrective Action Plan steps. These generally include:
- Implement technical policies and procedures to allow access only to those persons or software programs that have been granted access rights to information systems maintained.
- Implement procedures to regularly review records of information system activity, such as audit logs, access reports, and security incident tracking reports.
- Conduct accurate and thorough assessments of the potential risks and vulnerabilities to the confidentiality, integrity, and availability of ePHI.
- Develop a complete inventory of all its categories of electronic equipment, data systems, and applications that contain or store ePHI, which will then be incorporated into its Risk Analysis, and must complete a Risk Management plan.
What happens if I fail to complete my Security Risk Assessment? What happens next?
Failing to complete your annual Risk Assessment oftentimes means the organization will be required to complete a “robust” Corrective Action Plan (CAP) and often with at least two years of monitoring activity.
Have you ever doubted whether a small Billing Company or independent physician practice actually ever face penalties?
Keep in mind, a Business Associate is a ‘person’ or ‘entity’. This means there is no Billing Company too small or too large to comply with the Federal HIPAA regulations. Again, if you haven’t completed an accurate and thorough security risk assessment prior to that, you could also be penalized under ‘willful neglect’. This category alone is $50,000 per violation!
As we have stressed before, it is important for you to understand that every complaint or potential breach must be investigated by HHS/OCR. If you, a billing company, or other vendor, suspects a breach you must inform the covered entity (your client) and have a breach risk assessment completed to determine key factors and take action.
At Live Compliance, we make checking off your compliance requirements extremely simple.
- Completely online, our role-based courses make training easy for remote or in-office employees.
- Contact-free, accurate Security Risk Assessments are conducted remotely. All devices are thoroughly analyzed regardless of location. Conducting an accurate and thorough Security Risk Assessment is not only required, but is a useful tool to expose potential vulnerabilities.
- Complete set of HIPAA Policies and procedures built directly into your portal. Includes actionability, change management documentation, and Incident Response Policy to assist with your Corrective Action Planning. Easily share policies with staff with one click.
- Built directly into your portal, easily monitor where your workforce may be vulnerable with our Dark Web Breach Searches. Easily expose breach sources with ongoing searching of active employee email or domain ensuring continued awareness of potential breach exposure. Weekly automatic email notifications if new breaches are discovered.
- Short, informative, privacy awareness videos covering technical, administrative, and physical safeguards with topics such as Ransomware, Phishing, the Dark Web, Password Protection, etc. Delivered monthly with no logins required, empower your workforce to make conscious decisions when it comes to your organization’s privacy and security.
Don’t risk your company’s future, especially when we are offering a free Organization Assessment to help determine your company’s status. Call us at (980) 999-1585, or email me, Jim Johnson at Jim@LiveCompliance.com or visit www.LiveCompliance.com For more information please contact us at (980) 999-1585 or email us at support@livecompliance.com
For more information please contact us at (980) 999-1585 or email us at support@livecompliance.com

Apr 6, 2022 | Live Compliance, Partner
Don’t risk your company’s future, especially when we are offering a free Organization Assessment to help determine your company’s status. Call us at (980) 999-1585, or email Support@LiveCompliance.com or visit www.LiveCompliance.com