Jul 12, 2022 | Live Compliance, Partner
Whether you’re a one-person billing company or a multi-location organization, it’s possible that you’ve seen or heard of Malware and the potential risks associated with it and how it can cause major downtime and potential HIPAA violations due to breached information.
Criminals use malware to steal personal information, send spam, and commit fraud. Malware includes viruses, spyware, and other unwanted software that gets installed on your computer or mobile device without your consent. These programs can cause your device to crash and can be used to monitor and control your online activity. They also can make your computer vulnerable to viruses and deliver unwanted or inappropriate ads.
Here are a few, high-level quick steps you can take to spot and avoid Malware.
First, let’s talk security software.
Install and update security software, and use a firewall. Set your security software, internet browser, and operating system (like Windows or Mac OS X) to update automatically, and don’t forget to Back up your data regularly. Strong security software can prevent a hack or scam before it happens. You should install well-known software directly from the source. Sites that offer lots of different browsers, PDF readers, and other popular software for free are more likely to include malware. Read each screen when installing new software. If you don’t recognize a program or are prompted to install additional “bundled” software, decline the additional program or exit the installation process.
Don’t change your browser’s security settings and pay attention to your browser’s security warnings. Many browsers come with built-in security scanners that warn you before you visit an infected webpage or download a malicious file.
Next, watch what you’re clicking on.
Instead of clicking on a link in an email, type the URL of a trusted site directly into your browser. Scammers send emails that appear to be from companies you know and trust. The links may look legitimate, but clicking on them could download malware or send you to a scam site. Don’t open attachments in emails unless you know who sent it and what it is. Opening the wrong attachment — even if it seems to be from friends or family — can install malware on your computer.
Avoid clicking on pop-ups or banner ads about your computer’s performance! Scammers insert unwanted software into banner ads that look legitimate, especially ads about your computer’s health. Avoid clicking on these ads if you don’t know the source.
Your computer may be infected with malware if it:
-
- slows down, crashes or displays repeated error messages
- won’t shut down or restart
- serves a multitude of pop-ups
- serves inappropriate ads or ads that interfere with page content
- won’t let you remove unwanted software
- injects ads in places you typically wouldn’t see them, such as government websites
- displays web pages you didn’t intend to visit, or sends emails you didn’t write
Other warning signs of malware include:
-
- new and unexpected toolbars or icons in your browser or on your desktop
- unexpected changes in your browser, like using a new default search engine or displaying new tabs you didn’t open
- a sudden or repeated change in your computer’s internet home page
- a laptop battery that drains quicker than it should
At Live Compliance, we make checking off your compliance requirements extremely simple.
- Reliable and Effective Compliance
- Completely online, our role-based courses make training easy for remote or in-office employees.
- Contact-free, accurate Security Risk Assessments are conducted remotely. All devices are thoroughly analyzed regardless of location. Conducting an accurate and thorough Security Risk Assessment is not only required but is a useful tool to expose potential vulnerabilities, including those such as Password Protection.
- Policies and Procedures curated to fit your organization ensuring employees are updated on all Workstation Use and Security Safeguards in the office, or out. Update in real-time.
- Electronic, prepared document sending and signing to employees and business associates.
Don’t risk your company’s future, especially when we are offering a free Organization Assessment to help determine your company’s status. Call us at (980) 999-1585, or email me, Jim Johnson at Jim@LiveCompliance.com or visit www.LiveCompliance.com
For more information about DarkWeb breaches please contact us at (980) 999-1585 or email us at support@livecompliance.com

Dec 14, 2020 | Live Compliance, Medical Billing Software Blog, Partner, Support and Training
There are a few HIPAA items to focus on RIGHT NOW—before the end of 2020!
The U.S. Department of Health and Human Services (HHS) has designated the “Health Insurance Portability and Accountability Act” (HIPAA) as the national standard for protecting the privacy and security of health information (in 1996). This led to the Health Information Technology for Economic and Clinical Health Act (HITECH), which has a provision in it for audits, and the HHS Office for Civil Rights is responsible for carrying out HIPAA audits, and responding to complaints and breaches. Ignoring them is not an option!
A Risk Assessment IS NOT Enough
A risk assessment is only one element of the compliance process. You must also “implement security updates as necessary and correct identified security deficiencies.” In other words, you must act via a Corrective Action Plan (CAP) and follow the required risk assessment process.
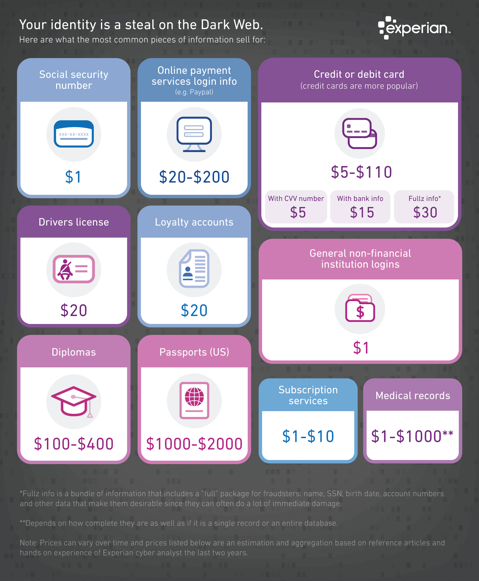
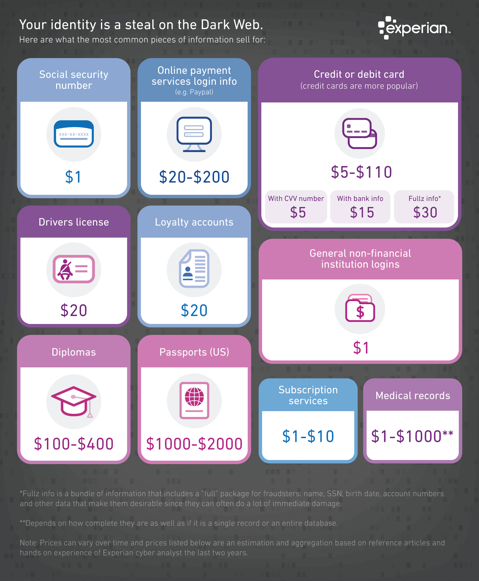
Dark Web
It is no secret that the “Dark Web” is a scary place to lose your information. So, what if it did happen and affected your entire company? Identity thieves get anywhere from $1-$1,000 for medical records, for each instance! So, how can you protect yourself and/or your organization?
Well, data breaches are becoming more common—sometimes which are out of your control—so carefully monitoring where you store and enter your passwords can be extremely beneficial to help minimize the risk of a hack and keeping personal or patient information protected.
One solution for this is the automatic Dark Web monitoring built into the portal of one of EZClaim’s partners, Live Compliance. Their solution helps keep an ‘eye’ on employees whose information was involved in a breach, and suggests next steps to take where the breach was found. Then, it allows your to conduct an accurate and thorough Security Risk Assessment. This is not only required, but is a useful tool to expose potential vulnerabilities, including those that involve password protection.
 So, what can I do to ensure this doesn’t happen to me or my organization? Well, Live Compliance makes checking off your compliance requirements extremely simple by providing:
So, what can I do to ensure this doesn’t happen to me or my organization? Well, Live Compliance makes checking off your compliance requirements extremely simple by providing:
● Reliable and effective compliance
● Completely online, our role-based courses make training easy for remote or in-office employees
● Contact-free, accurate Security Risk Assessments are conducted remotely. All devices are thoroughly analyzed regardless of location.
● Policies and procedures are curated to fit your organization, ensuring employees are updated on all workstation use and security safeguards in the office, or out. It is updated in real time.
● An electronic document is sent to employees and business associates
So, don’t risk your company’s future, especially when Live Compliance offers a FREE Organization Assessment to help determine your company’s status.
For additional details, call them at 980.999.1585, e-mail them, or visit their website at LiveCompliance.com
[ Article provided by Jim Johnson of Live Compliance ].
ABOUT EZCLAIM:
EZClaim is a medical billing and scheduling software company that provides a best-in-class product, with correspondingly exceptional service and support. Combined, they help improve medical billing revenues. To learn more, visit EZClaim’s website, e-mail them, or call a representative today at 877.650.0904.

Jul 14, 2020 | Administrative Safeguards, Uncategorized
Credit card collections are a BIG part of any successful medical practice, and there has been a shift, in the last decade, that more insurance policies are adding co-pays with higher deductibles—which makes getting paid even more challenging.1 One industry report said that “73% of physicians shared that it typically takes at least one month to collect a payment, and 12% of their patients wait more than three months to pay.”2 With the current trend, more medical practices and their billing departments (or outsourced billing firms) are going the route of processing payment via credit cards, which has its PROS and CONS.
In light of this new information, the following are a few pros and cons for credit card processing that we anticipate in the near future and some insights for choosing the best billing software that supports the credit card processing needs of medical practices:
- PRO: To protect against the dangers of stolen data, fraud, or other compromises in security, practices should seek out medical billing software that has credit card processing built-in, which can help safeguard against these dangers.
- CON: Security is a big risk, and a leak in data leading to stolen funds can end up in a physician paying out-of-pocket for the breach. It is also important to note that breach of credit card data is also considered a violation under the federal Health Insurance Portability and Accountability Act (HIPAA).
- PRO: Implementing credit card processing will reduce long waiting periods for payments from the majority of your patients, and will also reduce the additional effort your billing staff has to extend to collect on overdue notices.
- CON: Practices cannot require patients to share their credit card information to receive medical care, and even if patients do share their credit card information, physicians cannot continue to charge the credit card without a patient’s consent.
- PRO: Physicians can end the process of being a “line of credit” to unpaid or underpaid claims, and collect on funds immediately.
- CON: You will need to implement internal processes that include, but are not limited to proper personal information storage and security, establishing guidelines on maximum percentages charged per bill, and personal consent forms.
Overall, there are definitely MORE ‘PROS’ than cons for implementing credit card processing for your medical practice, and all the trends are pointing to this being the PREFERRED METHOD of payment in the near future. EZClaim is proud to announce that it will release an integrated credit card processing solution, EZClaimPay, that is backed by a national merchant services vendor. [ EZClaim will be sharing more details about EZClaimPay in the weeks to come, via their social media platforms, their monthly newsletter, direct communications, and more ].
In addition to the credit card collections PROS and CONS above, we reached out to one of our partners, Live Compliance, to gather some regulatory and security advice. They suggested the following:
- When accessing, transmitting, storing, or receiving any Protected Health Information (PHI), the Health and Human Services (HHS) Office of Civil Rights (OCR) mandates that you are to maintain HIPAA compliance.
- When accepting, processing, or maintaining credit card information and debit card information, you must ensure that your organization is PCI DSS compliant (Payment Card Industry Data Security Standard).
- In addition to the above Federal regulatory requirements, most states require privacy and security compliance requirements to be implemented, along with strict adherence to the privacy of Personally Identifiable Information (PII) and Breach Notification requirements.
For more information on your compliance requirements, visit Live Compliance for a Free Organization Assessment to identify and uncover your organization’s vulnerabilities.
If you are not a current customer of EZClaim, we would very much like to connect with you. You can either schedule a one-on-one consultation with our sales team, view a recorded demo, or download a FREE 30-day trial right now. For detailed product features or general information about EZClaim, visit our website at ezclaim.com.
[ NOTE: If you would like a quote on the upcoming merchant services, please e-mail sales@ezclaim.com your last three merchant statements. For more on our ongoing updates and industry news, you can follow EZClaim on Facebook and LinkedIn ].
Source Material:
1 – America’s Health Insurance Plans” report that there were 20.2 million co-pays in 2017, which was up tremendously from just over 1 million in 2005.
2 – Source: From InstaMed’s annual “Trends in Healthcare Payments” report.
> For more on this topic, read a previous article, “Why Do I Have A Balance? – Patient Payments”