Aug 15, 2022 | MedCycle Solutions, Partner
By Ann Knutson, CPC-A
The healthcare revenue cycle includes all administrative and clinical functions that involve capturing, managing, and collecting the provider’s/facilities revenue. The cycle includes three distinct parts of the practice/facility that’s referred to as the front-end, middle, and back end. Unfortunately, most of the time there is little coordination between the three areas which can lead to more claim denials and lost revenue for the practice/facility. Therefore, adding a revenue integrity team to your practice/facility dramatically improves operational efficiency, compliance measures, and reimbursement rates. Members of the team must have extensive knowledge of and be familiar with the complete healthcare revenue cycle.
In order to foster collaboration between all three areas of a practice/facility that affect the revenue cycle, specific training needs to be implemented for staff, along with coding and documentation education for providers.
Specific staff training includes:
- Keeping up to date on billing requirements, such as coding guidelines, billing regulations, and insurance payer policies.
- Reimbursement updates, such as data showing rate of reimbursement vs. denials/rejections.
- Key performance indicators, such as data regarding common billing or coding errors leading to claim denials and rejections.
- Job expectations, such as all billing employees must know every aspect and function of their job in detail.
Provider education involves:
- Chart reviews to verify proper documentation.
- Quarterly meetings regarding coding guidelines, payer rules, and the importance of medical necessity.
Furthermore, creating templates and tip sheets for billers, coders, and providers improves operational efficiencies, clean claim submission, and proper provider documentation. It also decreases claim denials and puts everyone in the practice/facility on the same page.
In addition, the collaboration between coders and the accounts receivable team is crucial to improving reimbursement rates, the outcome of claim appeals, and compliance with regulations. It can also help to reduce the number of claim denials and rejections. Plus, medical coders are able to share their expertise regarding regulations and proper coding with the Accounts Receivable (AR) team members. This helps the AR team with reconciling claim rejections and denials along with properly submitting appeals. On the other hand, the AR team can inform coders of the current codes or coding combinations that are being rejected or denied by payers. With this vital information, coders can make the required coding and billing changes as they enter the charges and submit the claims. This can greatly improve the rate of clean claims submission. (AAPC, 2021)
Therefore, it’s in the best interest of a practice/facility to implement a revenue cycle management team that is familiar with the entire revenue cycle, fosters collaboration between all areas of the practice/facility and providers, and maintains open communication between all departments in order to maximize revenue cycle efficiency and reimbursement. For assistance with maximizing your revenue cycle efficiency, please contact us at MedCycle Solutions.
For more information about maximizing revenue cycle efficiency, please visit www.aapc.com.
Ann Knutson, CPC-A is an Accounts Receivable Specialist at MedCycle Solutions, which provides Revenue Cycle Management, Credentialing, Outsourced Coding, and Consulting Services to a number of healthcare providers in a variety of specialties. To find out more about MedCycle Solutions services please visit www.MedCycleSolutions.com.

Apr 5, 2021 | AMBA National Conference, Medical Billing Software Blog, MMBA Chapter Meetings, Support and Training
In this interview with a medical billing expert and co-owner of Elite Billing Resolutions, Vicky Greenwood, we talk about dealing with the challenges in owning a billing company, some important skills that every medical biller needs, and the value of choosing the right medical billing software. In our time speaking with Vicky, we focused on topics that will aid, contribute, and help grow the skills of the medical billing community. We at EZClaim believe in highlighting the best practices in the industry and sharing those with the larger community. We encourage you to consider these insights, and then let us know what topics you would like to learn more about.
EZCLAIM: When did you get into medical billing?
VICKY: “I started in 1994, and at the time we were working on a dinosaur of a system called, “Signature.” We would have to wait overnight to process the entire day’s work. Then we would return in the morning to see if there were any errors in the batch or denials in the claims, which meant being accurate in entering information was essential. Outside of that, we kept all our paperwork in filing cabinets, and they needed to be sorted and organized by date. If a date was off in the filing system it could take the better part of a day to find a patient’s claim. The difference between then and now is night and day. I am definitely thankful for technology.”
EZCLAIM: Why did you start Elite Medical Billing?
VICKY: “We started Elite Medical Billing because we wanted to be able to directly impact our medical practices with the services we provided, and we wanted the freedom to enjoy doing it for our clients. I also knew that I was experienced in the field, was competent at my job, and enjoyed doing what needed to be done to get practices paid. Once I honed those skills and knew we could do it. We hired a lawyer and an accountant, then formed our company.”
EZCLAIM: What are challenges in starting a company?
VICKY: “First, you have to understand the value of time management and delegation. You don’t want to bite off more than you can chew. It is good to know when you need to ask for help. Next, you want to find good staff. I look for people who have the right attitude about the job first and have the characteristics to be proactive and work hard. Then, I look for experience in the field, learning if they had hands-on experience with claims, denials, and coordination of benefits is part of that. At the end of the day, my staff are my [company], and fortunately, most of my staff have been with me from the beginning.”
EZCLAIM: Why did you choose EZClaim?
VICKY: “We had a client who needed software and, being a smaller company, we needed cost-effective software with strong tech support. When we searched on Google for “easy to use medical billing software,” we found EZClaim. We were won over by the first phone call. Since then, we have been reminded of how great a decision that we made. The simplicity by which you can enter the information, process new patients, and ‘claim them’ within minutes is invaluable. That combined with the great customer service—that answers our questions most often on the first call with detailed answers—and video tutorial support is why we will continue to use and promote the software.”
EZCLAIM: Are you a member of AMBA and MMBA?
VICKY: “We joined the MMBA and AMBA in 2016 to help us certify our billing company. That process and the training, testing, and materials were amazing pieces of helping us get established and grow. In addition, the expos, webinars, and online support offer an abundance of information. Of course, the annual expos are both informative and a great work trip for team building and fun. We make it annually to the MMBA, but our next big goal is to go to the AMBA in Las Vegas!”
EZCLAIM: Have some final thoughts to offer fellow medical billers and business owners?
VICKY: “As a medical biller and owner, you have to be willing to talk with physicians. You need to show them the vouchers and documentation of your work. And it is important to communicate how they bill and how they can be sure to properly classify to get paid. You need to review what they have done in the past and how they can improve in the future by training staff.”
“You can also add value by making them the good guy and yourself the bad guy when dealing with patients and getting paid. We allow patients to call us directly, we answer the questions, and tell them how much they have to pay—then we forward the call to the office. Remember, at the end of the day, you have to show them the money. They work hard and they deserve to get paid.”
ABOUT EZCLAIM:
As a medical billing expert, EZClaim can help the medical practice improve its revenues since it is a medical billing and scheduling software company. EZClaim provides a best-in-class product, with correspondingly exceptional service and support. Combined, EZClaim helps improve medical billing revenues. To learn more, visit EZClaim’s website, email them, or call them today at 877.650.0904.

Feb 9, 2021 | Administrative Safeguards, Cloud Security, Live Compliance, Medical Billing Software Blog, Partner
Ransomware hackers target medical billing companies, and it CAN AFFECT your entire company! (Ransomware is a type of malicious software designed to block access to a computer system until a sum of money is paid.)
Often out of one’s control, ransomware hackers target medical billing companies because of the tremendous value of the data. BUT, there are steps that CAN BE TAKEN to protect you, your company, and your patients and/or clients.
NetWalker Ransomware, for example, gained notoriety for targeting hospitals and healthcare providers with e-mails claiming to provide information about COVID-19. (The e-mail usually has an attachment that downloads the ransomware from a remote server when clicked on.) The thing is, this is very lucrative for identity thieves since medical records information sells anywhere from $1-$1000!
As the number of healthcare providers taking advantage of Telehealth continues to increase—now outnumbering in-person visits—the number of ransomware attacks continues to increase as well. This means Billers and Providers must be aware of the programs that are used on their machines and ensure necessary steps are taken to safeguard against hackers and attacks.
How can you protect yourself and/or your organization?
- Carefully monitoring where you store and enter your passwords can be extremely beneficial to help minimize the risk of a hack and keeping personal or patient information protected.
- Routine password changes and monitoring where you store and enter your passwords can be extremely beneficial to help reduce the risk of becoming a victim to a hacker. Passwords should be long, unique in characters, capitalization, and alphanumerical.
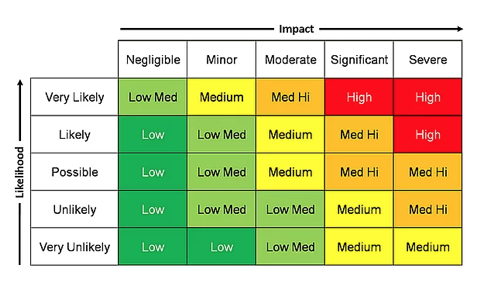
- Have you had an accurate and thorough Security Risk Assessment and/or penetration testing? If you haven’t completed an accurate and thorough security risk assessment, you could also be penalized under ‘willful neglect’ (this category alone is $50,000 per violation!) in addition to the higher risk of ransomware attacks.
- If you believe you might have revealed sensitive information about your organization, report it to the appropriate people within the organization, including network administrators. They can be alert for any suspicious or unusual activity.
- The strength of your passwords directly impacts your online security.
Live Compliance can help. They aggregate breaches which enables you to assess where personal data has been exposed. Dark Web scanning is built right into their Portal, and it allows you to keep an eye on employees whose information was involved in a breach, where the breach took place, and then suggest the next steps to take.
At Live Compliance, they make checking off your compliance requirements extremely simple and to ensure this doesn’t happen to you or your organization:
- Reliable and effective compliance
- Completely online, our role-based courses make training easy for remote or in-office employees
- Contact-free, accurate Security Risk Assessments are conducted remotely. All devices are thoroughly analyzed regardless of location. (Conducting an accurate and thorough Security Risk Assessment is not only required but is a useful tool to expose potential vulnerabilities, including those such as password protection.)
- Policies and procedures curated to fit your organization ensuring employees are updated on all workstation use and security safeguards in the office, or out of the office—all updated in real-time
- Electronic, prepared document sending and signing to employees and business associates
So, don’t risk your company’s future on ransomware hackers. Contact one of EZClaim’s partners, Live Compliance, especially since they are offering a FREE Organization Assessment to help determine your company’s status. E-mail them, visit their website at LiveCompliance.com, or call them at 980.999.1585.
For more information about EZClaim’s medical billing software, which provides a best-in-class product with correspondingly exceptional service and support, e-mail, visit their website, or contact them at 877.650.0904.
[ Article contributed by Jim Johnson of Live Compliance ]
Oct 13, 2020 | HIPAA, Live Compliance, Medical Billing Software Blog, Partner
New HIPAA compliance requirements are coming!
In an effort to make the HIPAA Privacy Rule as easy to understand as possible, the Office for Civil Rights (OCR) has come up with a list of rules that clearly explain what Business Associates are now “directly liable” for. As OCR Director Roger Severino explains, “We want to make it as easy as possible for regulated entities to understand, and comply with, their obligations under the law.” The list consists of ten rules that, if failed to follow, can result in penalties and monetary fines.
[ Note: Check out our previous post to access this list ].
Immediate Requirements:
As we enter the fourth quarter of the year, you may be wondering what immediate requirements should a Business Associate complete before the end of the year?
One of the most important rules also includes information about Business Associates, and their need for proof of satisfactory assurance when the covered entity requests this of them. Satisfactory assurance is crucial, because it ensures the Business Associate is HIPAA compliant, and therefore, must also be in the form of a contract.
The Satisfactory Assurance contract is oftentimes outlined in the form of a questionnaire, and requires the Business Associate to disclose the date of completion for various compliance requirements.
These include distribution and completion of workforce HIPAA training, implementation and distribution of policies and procedures, Business Associate documentation, and completion of an annual HIPAA Security Risk Assessment.
Are You Prepared?:
If a Covered Entity requests this proof from your organization, would you be able to successfully complete it without outdated completion?
If you are uncertain that your organization would be able to easily and efficiently provide that documentation, you may be facing thousands of dollars in fines for each vulnerability!
HIPAA Compliance Myths:
False: The security risk analysis is optional for small providers: All providers who are “Covered Entities” under HIPAA are required to perform a risk analysis. In addition, all providers who want to receive MU, and MIPS incentive payments must conduct a risk analysis.
False: Our office uses the Cloud, so we don’t need a risk assessment: Even if you have a fully HIPAA compliant cloud vendor, your patient data (ePHI and PII) still must go through all your systems to get to the cloud. So, you are still required to perform technical, administrative, and physical security risk analyses.
False: Our EHR makes us compliant, so we’re fine: While your EHR may provide excellent privacy and security features, it definitely doesn’t exempt you from the HIPAA security requirements.
Live Compliance helps their clients meet the ever changing and complex HIPAA State and Federal regulations. They protect the information they are entrusted with, and ensure their clients pass any Health and Human Services audits. If you are unsure or need assistance, call Jim Johnson with Live Compliance at (980) 999-1585.
Live Compliance is a partner of EZClaim, a medical billing software company. For more details about their solutions, visit their website at ezclaim.com.
Aug 11, 2020 | Administrative Safeguards, Live Compliance, Partner
Failing to implement HIPAA causes a large fine for a small-town North Carolina health services provider. They were fined $25,000 for multiple, easily avoidable, HIPAA violations for “longstanding, systemic non-compliance” with the HIPAA Security Rule. [ Note: The provider is a part of a health center that offers discounted medical services to the underserved population in rural NC, and the fines were reduced in consideration of this, but it still resulted in a significant monetary loss ].
In 2011, Metropolitan Community Health Services (Metro), doing business as Agape Health Services, filed a breach report regarding “the impermissible disclosure of protected health information to an unknown email account.” The breach affected over 1,200 patients!
In addition to the large monetary penalty, the practice is required to develop and adopt a corrective action plan (which includes two years of thorough monitoring) after the Office for Civil Rights (OCR) discovered that Metro failed to conduct a thorough and comprehensive HIPAA Security Risk Assessment and Analysis. In addition, Metro did not implement a single HIPAA Security Rule Policy and Procedure for the health center. Possibly worst of all, Metro failed to provide workforce members with HIPAA Privacy and Security Awareness training until 2016!
Patients must trust with who they share their personal, private, and protected health information. A breach such as this is obviously devastating for the patient, in addition to their doctor’s reputation. So, how can physicians ensure that they are meeting the HIPAA requirements and have proper safeguards in place to avoid this sort of breach?
First off, an accurate and thorough Security Risk Assessment and Analysis must be conducted to expose and target any potential administrative, physical, and technical vulnerabilities. Doing so highlights any major flaws in a practice’s administrative and technical safeguards, and accentuates the policies and procedures that the practice needs to implement.
In addition to that, the designated HIPAA Privacy and Security Officer must ensure that ALL employees complete HIPAA Workforce training. All employees of the practice, including the physicians, must take HIPAA training to ensure employees have a clear understanding of the HIPAA Privacy Rule and actionable policies and procedures.
So, remember, healthcare organizations and their vendors have a responsibility to be HIPAA compliant, and that starts by performing, updating, or reviewing an accurate and thorough Security Risk Assessment covering your technical, administrative, and physical safeguards. This will help uncover any vulnerabilities, and help you understand what information is being transmitted, shared, and how it is being transmitted.
TAKEAWAYS AND THINGS TO CONSIDER:
- Complete a Security Risk Assessment and establish a Corrective Action Plan that is accurate and thorough.
Remediate any potential risks or vulnerabilities.
- A Security Risk Assessment will target vulnerabilities related to what is potentially exposing Protected Health Information (PHI)
- Develop actionable policies and procedures that clearly outline disclosures of PHI
- Ensure all employees have a clear understanding of the HIPAA Privacy rule and its policies and procedures
Live Compliance provides everything you need to become and maintain your organization’s HIPAA compliance requirements. All policies and procedures can be edited and shared directly with staff from your staff portal. Training are delivered and monitored within your portal, can be customized, role-based, and be accessed anytime and from anywhere. You can also easily send and monitor HIPAA training with one click.
Failing to implement HIPAA can cause tremendous problems and use precious resources and time to implement. Live Compliance makes it 10X easier than trying to do it on your own.
So, take advantage of Live Compliance’s FREE Organization Needs Assessment to understand your immediate compliance needs. For additional details, e-mail Jim Johnson (at jim@livecompliance.com), call (980) 999-1585, or visit their website at livecompliance.com/oa
Live Compliance is a partner of EZClaim, a medical billing software company. For more details about their solutions, visit their website at ezclaim.com.
[ Written by Jim Johnson, President of Live Compliance ]